Audit Highlights
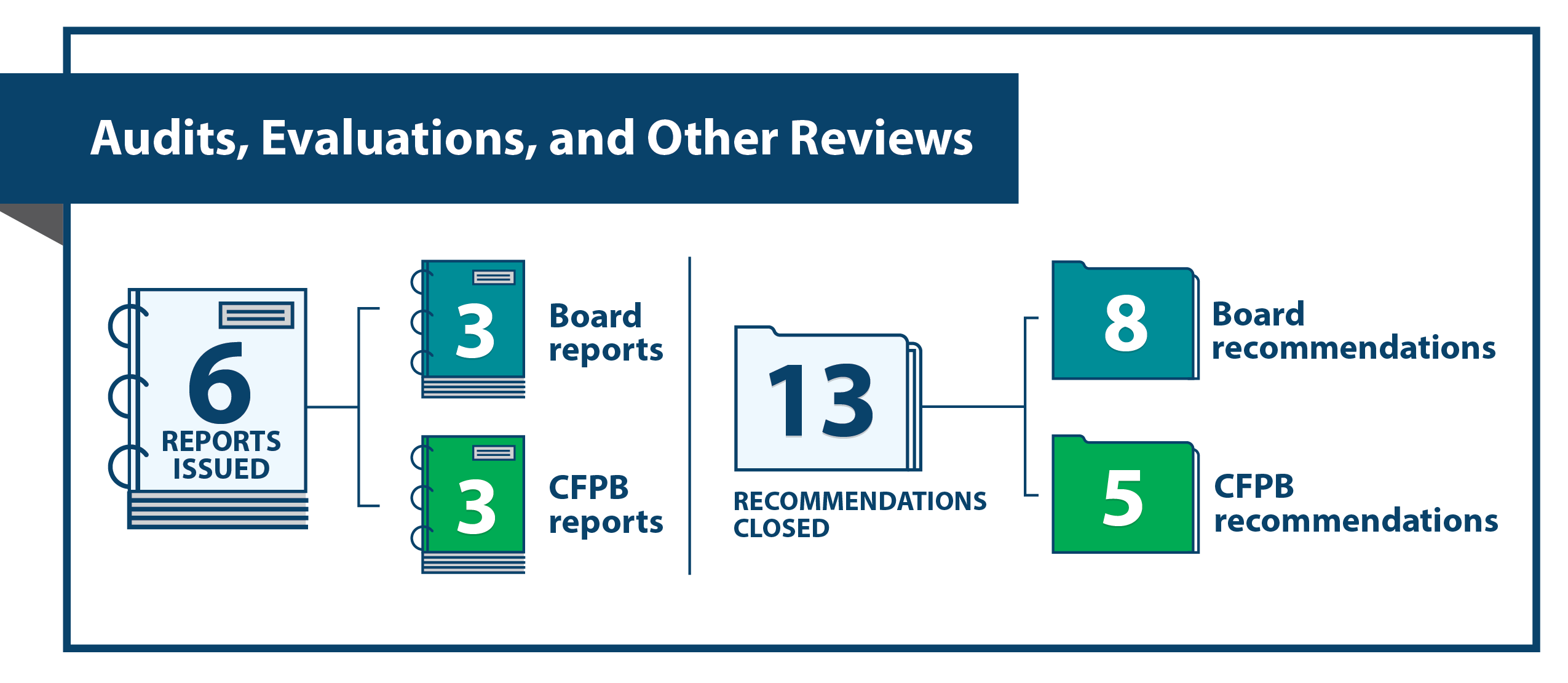
The following are highlights of our work during the April 1, 2025–September 30, 2025, semiannual reporting period.
 The CFPB Can Improve Its Safeguards for Protecting Confidential Supervisory Information
The CFPB Can Improve Its Safeguards for Protecting Confidential Supervisory Information
The CFPB's guidance for safeguarding confidential supervisory information (CSI) does not sufficiently limit access to it or establish expectations for assessing the severity of CSI breaches and enforcing consequences for responsible employees.
The Board Can Strengthen Its Travel Card Program
The Board has established and maintained certain controls for its travel card program, but its internal control system needs to be improved to ensure that employees comply with travel requirements.
The Board Can Enhance Its Approach to the Cybersecurity Supervision of Community Banking Organizations
Procedures for information technology (IT) examinations of community banking organizations (CBOs) do not reflect the evolving IT and cybersecurity risk environment and need to be updated. In addition, Federal Reserve Banks have varying approaches to training examiners who conduct CBO IT examinations and completing and retaining documents used to scope such examinations.
The CFPB Can Improve Its Records Management Program
The CFPB is beginning to prepare for the required transfer of permanent records to the National Archives and Records Administration but has not yet provided CFPB divisions with instructions or a timeline for the transfer. In addition, the CFPB should conduct routine formal evaluations of its records management program to help promote effective records management.
